DC612 Meetings
Defcon 612 meeting posts.
Thursday, June 11th – 6:12pm @Virtual Only
DC612 June Meeting – Live From the Interwebs
UPDATE: The June DC612 Meeting URL is: https://cafe.cyberia.club/random-meeting-name-DC612
Feel free to lurk until the meeting officially starts at 6:12pm

This is another virtual-only meeting. We will again be using Jitsi, courtesy of our friends at Cyberia. Please forgive any technical issues as we continue to figure out this new platform.
This Month, Starless will be speaking on a subject of growing relevance.
“Mask Hacks, or How to Be A Good Neighbor in A Pandemic”
“Everything you’re supposed to buy is sold out at Target. How can you use household materials to make your mask the best possible, given the circumstances? Damned if I know. But! Here are some guesses. I’m not qualified to give this talk, but I’m too mad about people not solving these problems any better to do nothing. Join me at my work desk for materials ideas, mask fitting opinions, a nose wire bending demo and maybe even a filter construction demo, if you ask nice.”
This Month we’ll talk Masks, Institutional Racism and provide resources to help us all become better Anti-Racists.
The meeting URL will be shared an hour before the meeting is set to start on Thursday. See you all there!
-Kat
Thursday, March 7th – 6pm @ Wilde Roast Cafe
Important Update! The location has changed but the date remains the same from our last announcement (it is the first Thursday this month). Our usual spot is closed for renovations, so we will be returning to our old stomping grounds at Elsie’s! We won’t be in the front room near the entrance it sounds like, but rather in the back room in the dining area. Ask staff if you need directions. There is usually plenty of free parking, and the side road has curbside parking as well.
We will have two Hacker friendly games available for play.
C.I.A. (https://www.kickstarter.com/projects/mmasnick/cia-collect-it-all)
– A competitive card game based on the CIA’s declassified training game: Collection Deck.
Get Loot (https://shop.hak5.org/products/get-loot)
– GET LOOT is a 3-5 player competitive hacking game where your goal is to exfiltrate (steal) loot while sabotaging your rivals with strategic crypto-locks and Hak5 themed cyber attacks!
Don’t forget to bring your lock pick sets! We will have a collection of practice locks to play with through out the evening.
Rescheduled To: Monday February 11th – 6pm @ Wilde Roast Cafe
Hey Hacker Fam
Our February Meeting is rolling up to you a week early – thanks hallmark holiday 🙁
On tap this month we have a topic that we can all relate to.
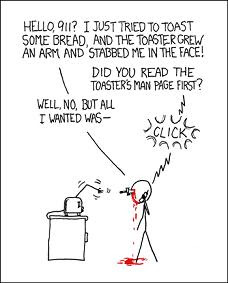
This week at DC612 we’re talking DOCUMENTATION! and what its really good for? Or more importantly, how do we feel about it?
(Most people) Don’t like it
(Most people) Don’t like to write it
(Most people) Don’t like to sift through it
Then again (Most people) Really don’t like when it’s not there
Then again (Most people) Really don’t like it when it’s there and it’s wrong
This Thursday, come on out for our speaker Eric. His talk will cover a history of documentation, reflections on why we document and ways we can do it better.
Hope to see all you there!
-Kat
DC612 – Thursday February 9th – 6pm @ Wild Roast
This February we welcome Josh More as he presents to us,
Captivating Security – Safety versus Passion
After decades of trying to get noticed, infosec has arrived in business. We have the attention of senior management and boards. We finally have budget. We finally have power. What are we going to do with it?
We stand at a fork in the road.One path is well trodden. Paved with best practices, metrics, and models, we can follow other industries. By restricting capabilities and focusing on compliance with regulations, standards, and monitoring efforts, we can merge with mature industries like banking, insurance, and the highly structured governmental/military ways of doing things. This path is safe.
The other path is rocky and overgrown. This is the path walked by those who must deal with complexity. Using nature conservation as a model, this path involves constant exploration and experimentation. Those on this path must use creativity and resilience to address the complexities involved in the overlap of economics and ecologies. This path is risky … but with risk comes reward.
Josh More is actively researching this second path, using the history of endangered species conservation and captive breeding as a model for where our industry could go. Though a harder path and less certain, the advantages of resisting the easy path could be tremendous. This is extremely early stage research and Josh would appreciate frank discussion around the ideas involved to help guide future research and maximize the utility of the eventual book.
Additionally we will be discussing the launch of DC612 Projects, reviewing the categories and announcing the SME’s.
See you all at the Wilde Roast!
DC612 – Tuesday, October 11th – 6pm @ the Wilde Roast
DC612 brings you:
“Many threat vectors have been assessed in the medical device world, but there is no available work on extortion as a threat vector. By mapping the extortion attack surface area of a given medical device, understanding the threat actors, and looking into how the exploits would happen, I made a tool to help understand the problem better. My hope is that a medical device company would use this information to roll extortion threat assessment into their existing safety evaluations.” – Judd Larson